Prosecutor: NJ man paid $20K to kill 14-year-old he sexted
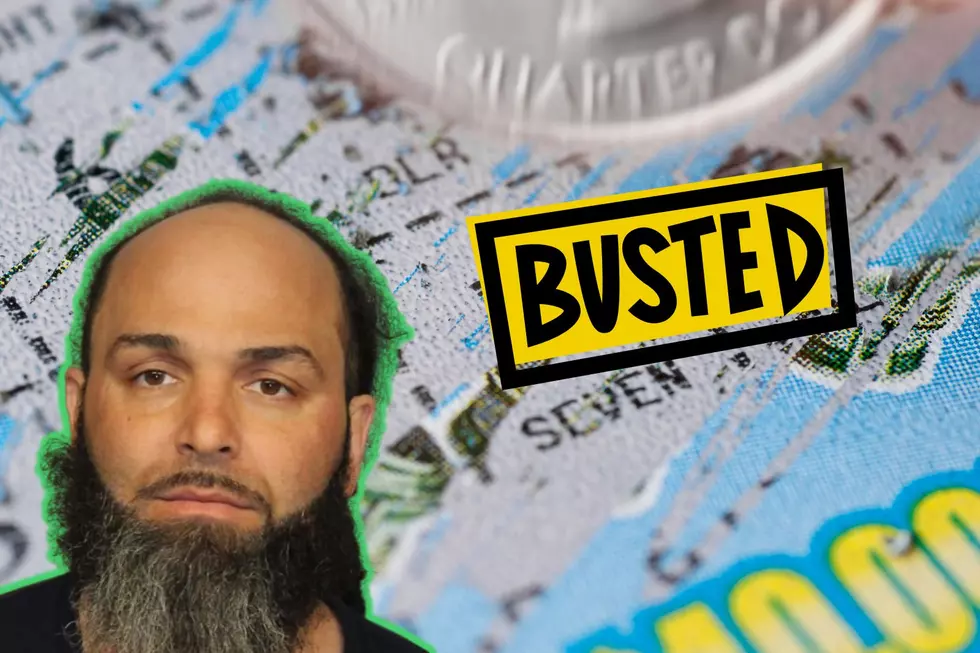
A 31-year-old New Jersey man facing child pornography charges paid $20,000 worth of bitcoin to have someone kill a 14-year-old whom he had been found sexting, according to federal prosecutors.
John Michael Musbach, of Haddonfield, has been indicted on a count of murder-for-hire, stemming from exposed transactions on the “dark web” in 2016. He was arrested and initially charged last August.
The year before, Musbach had begun chatting online with the child who was then 13, prosecutors have said.
He began exchanging sexually explicit videos and photographs with the minor, whose parents eventually found out about it and notified police.
Musbach, who lived in Galloway at the time, was arrested by the Atlantic County Prosecutor’s Office in March 2016 and faced child pornography charges.
In October 2017, Musbach pleaded guilty to endangering the welfare of a child by sexual contact and was sentenced in February 2018 to a two-year suspended sentence with parole supervision for life.
Then in early 2019, an informant brought the apparent hit attempt to the attention of authorities.
Investigators found that after months of internet searches in late 2015 and early 2016 that included “child grooming law,” “where to be chloroform,” “NJ gun shows” and “Not guilty by reason of insanity,” Musbach had asked online about either buying a gun or hiring someone to kill a teen.
After being reassured that “14 years is acceptable” for a hit, Musbach converted his money and deposited $20,000 worth of cryptocurrency in May 2016, according to a criminal complaint filed last summer.
He got worried when he hadn’t heard anything about a week later. When the supposed hitmen agency tried to shake him down for another $5,000, he tried to come up with it but couldn’t convert it in time — a couple days later, he tried to cancel the hit and get a refund.
At that point, Musbach got a message that read “I am sorry to disappoint you. Unfortunattely [SIC] our site is a scam, and we pass customer and target information to law enforcement.”
The site operators then tried to blackmail him for additional money before the exchange eventually did make it to the attention of law enforcement.
Musbach’s identity was confirmed through various online screen names and by following the money from his bank account to the purchase of bitcoin used to pay for the hit, according to Acting U.S. Attorney Rachael A. Honig.
DID YOU KNOW: New Jersey has a volcano!
South Jersey child porn bust
NJ towns that actually cut property taxes in 2020
More From New Jersey 101.5 FM